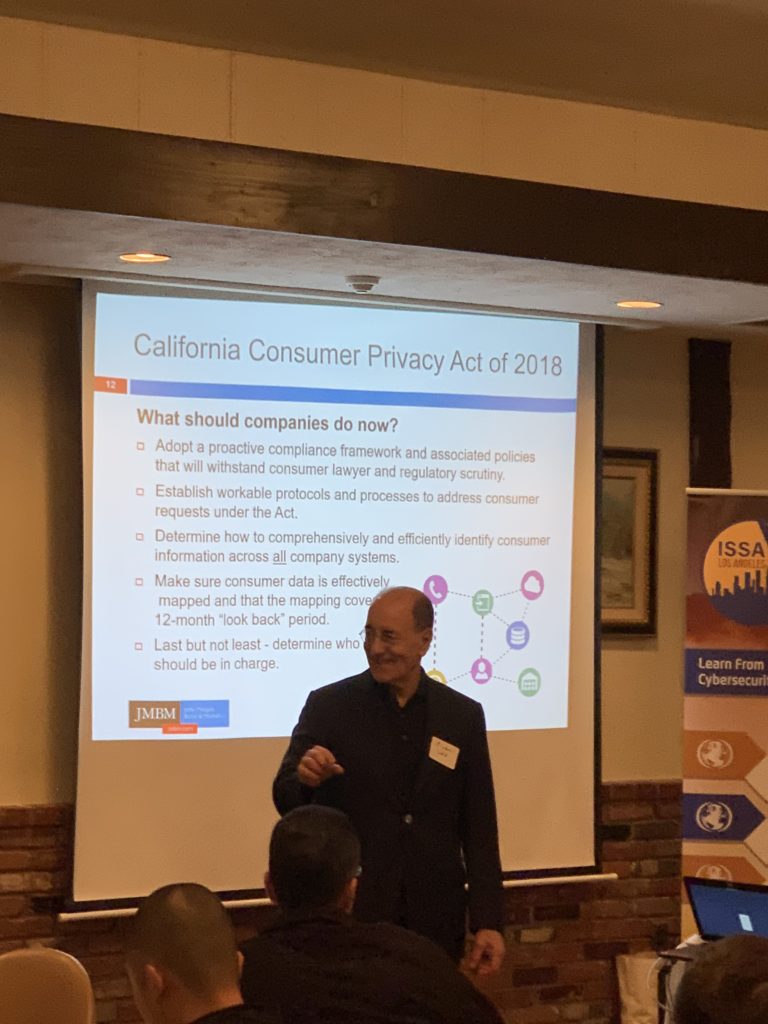
Topic: California Consumer Privacy Act (CCPA)
The California Consumer Privacy Act of 2018 is the most comprehensive law of its kind ever enacted in the United States, setting forth rules for companies that buy, collect, transfer or sell consumers’ personal information. Because of the size and reach of the California economy – the 6th largest in the world – and the number of companies that may need to comply – estimated at about 500,000 worldwide – the CCPA is effectively a national, if not international, law. This program will address the salient features of the CCPA, who must comply, the new rights consumers have under the CCPA, legal exposures for violations, likely impacts of the law, and what companies should do to comply with the law.
Speaker: Michael Gold

Michael Gold is co-chair of JMBM’s Cybersecurity and Privacy Group and counsels businesses in a wide variety of matters, including data breach responses and investigations, crisis management, development of computer-based information retention systems, forensic investigations of computer systems, and computer and internet privacy matters.
Michael assists clients in developing and implementing information management and governance best practices and developing policies and compliance structures for protecting personal and company information. He counsels clients on information security and privacy law compliance issues; assists clients in developing policies and processes to comply with information security and privacy laws (including the E.U.’s General Data Protection Regulation, the California Consumer Privacy Act of 2018, and other state and industry-sectoral privacy laws in the U.S.); negotiates technology agreements relating to information security and privacy; and defends litigation and arbitrations, including class actions, arising from data breach and privacy claims.
Michael was named one of California’s “Top 20 Cyber – Artificial Intelligence Lawyers” by the Daily Journal (2018), one of the “Most Influential Lawyers: Digital Media and E-Commerce Law” by the Los Angeles Business Journal, and has been designated a “Top Rated Lawyer in Technology Law” by Martindale Hubbell. He is the author of the upcoming Bloomberg BNA portfolio Enterprise Cybersecurity Governance, and co-author of the Bloomberg BNA Portfolio Records Retention for Enterprise Knowledge Management.